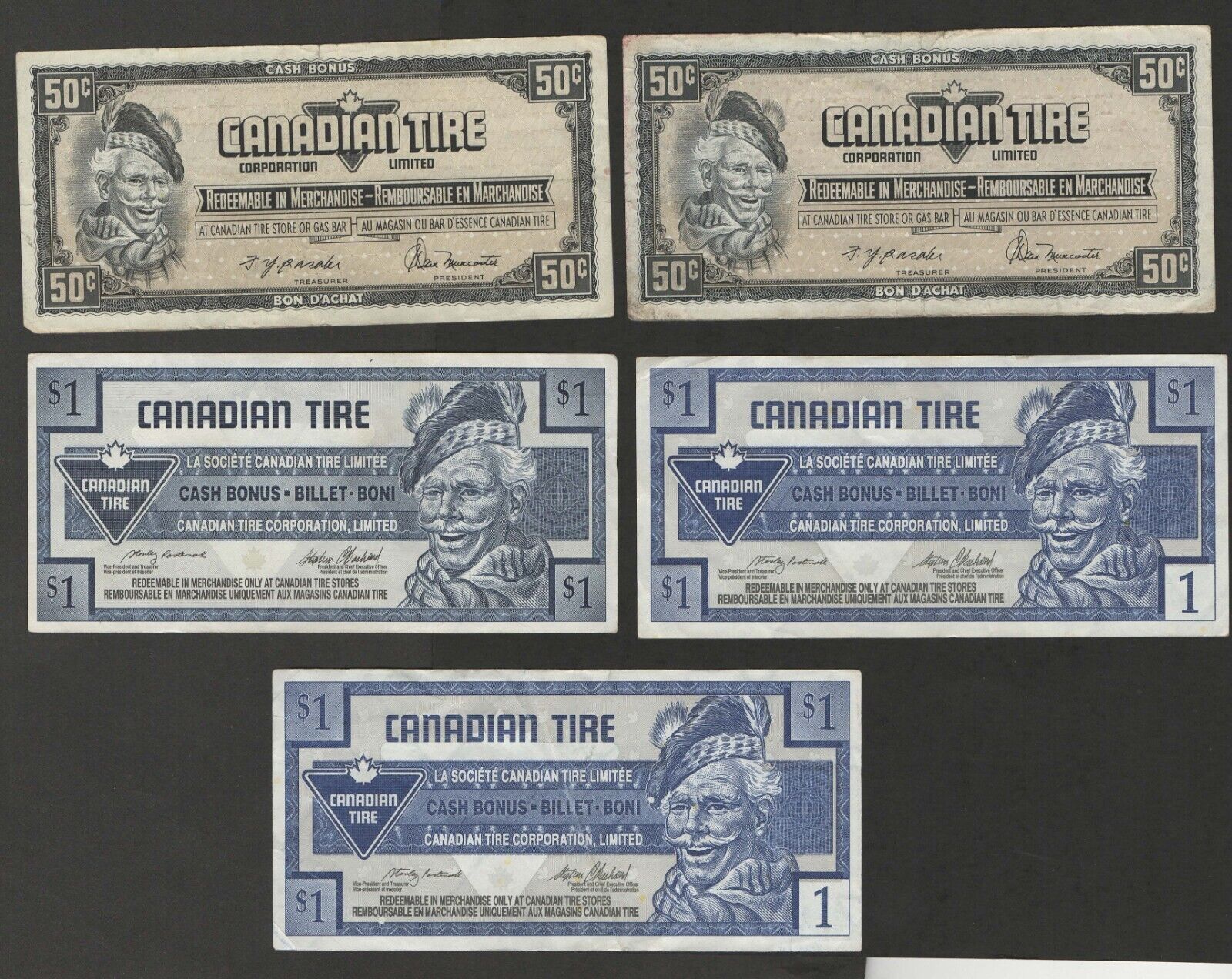
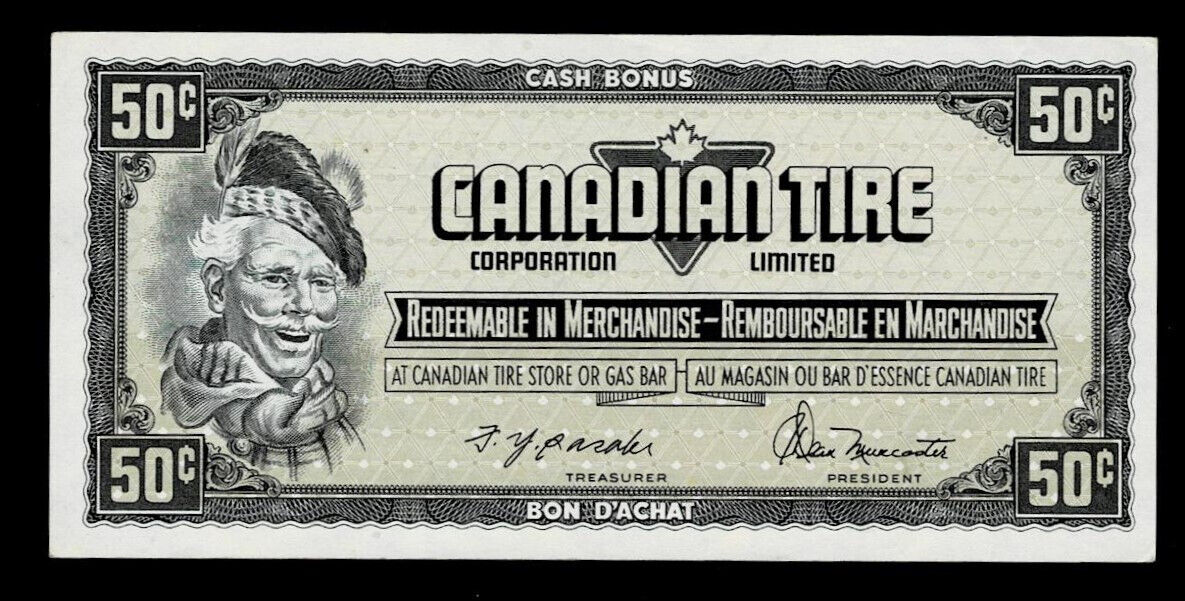
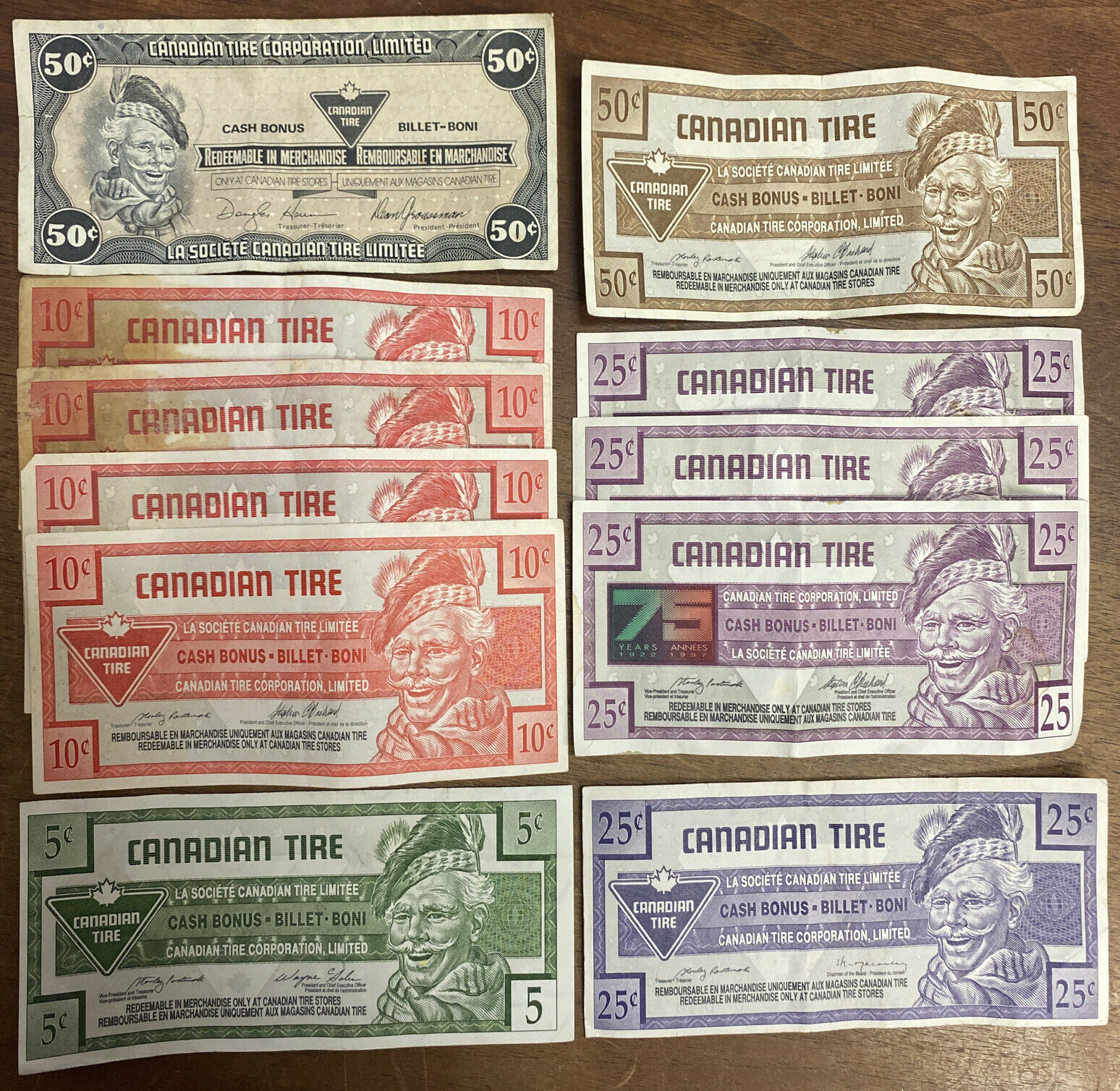
Coins & Paper Money
More ProductsBusiness & Industrial
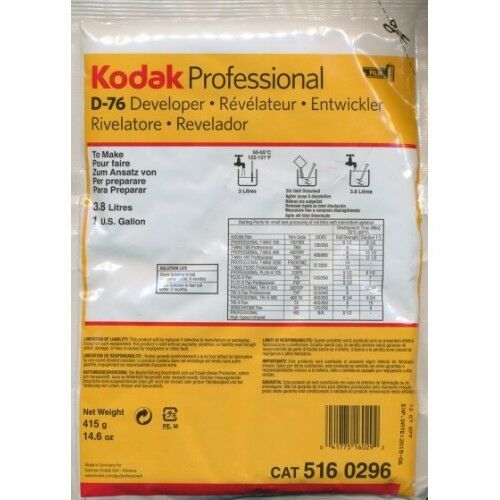
More ProductsCameras & Photo
More ProductsClothing, Shoes & Accessories
More Products
We are a professional online business in the world. We offer wholesale products for buyers around the world.
We do not collect personally identifiable information (for example, name, address, phone number, and email address), also referred to herein as "personal information," unless you provide it to us voluntarily.




All orders are treated with the utmost care to meet the needs. Our customers appreciate the importance of your purchase, which is why we only sell new, unopened, unused products that order us directly from the manufacturer. Our customers expect, and will always receive, the high quality product when ordering with us. Our goal is to provide our customers the right products at the right price, delivered in time.
We have a powerful customer service team that keeps an eye on the entire sales process. The team is always ready and happy to help you, resolve your returns and replace, and listen to your complaints. Our service team sticks to its guideline.
Copyright © 2024 www.positiever.info . A division of Altru Enterprise Pty Ltd. ACN 146 181 991